Block Ciphers Modes of Operation - LinkedIn SlideShare.
A hash is used to take a message of any length and produces a fixed-sized output length using a hash function. For example the SHA256 hash function produces a 256-bit hash value regardless of the input message length. Given a hash value it is not.
A good essay writer is a qualified professional with the necessary hard and soft skills. A one-on-one meeting allows us to find flexible and outgoing authors with great time-management qualities and a genuine passion for writing. 40% of applicants get to the next round.
The counter mode of operation is designed to turn block ciphers into stream ciphers, where each block is encrypted with a pseudorandom value from a “keystream”. This concept achieves this by using successive values of an incrementing “counter” such that every block is encrypted with a unique value that is unlikely to reoccur.
Abstract This thesis is dedicated to symmetric cryptographic algorithms. The major focus of the work is on block ciphers themselves as well as on hash functions and message.
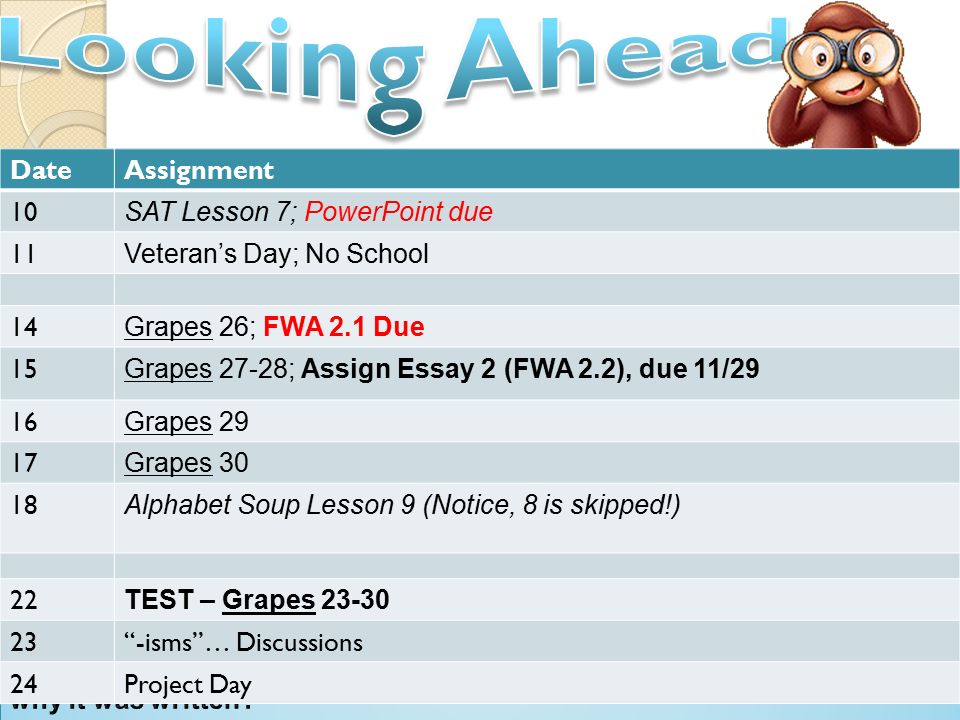
A comparative essay can be used in formal writing assignments and it can also be the basis for various research assessments. A comparative essay is created through pertaining precise points of comparison. These points should be backed by actual researchers, factual information, and other reliable evidence. Block Comparative Essay Example.
Block pattern can be structured in a different manner as well. Instead of the separate paragraph for each point, you compare, you can set out one section to name their similarities and a second paragraph to analyze dissimilarities point by point.
The next part of compare and contrast essays is a body, and here are tips on how to write a good 5 paragraph comparing and contrasting essay. An effective outline prevents from the case of facing writer’s block.